Attackers Are Impersonating Your Organization Right Now. Your Email Security Is Just Watching.
Impersonation, Spoofing, and Business Email Compromise Attacks Are Worth Billions.
Your domain could be at risk.
The email arrived from your company's CFO. The signature was correct. The writing style was perfect. The request was urgent but not unusual: "Wire $75,000 to this account for the acquisition closing. Vendor needs payment today."
Your accounts payable manager processed it immediately.
The CFO never sent that email. Attackers did. They spoofed your domain because you had no DMARC protection—or worse, you had DMARC set to "monitor only," which gave you visibility into the attack but did absolutely nothing to stop it.
Welcome to 2026, where 71% of domains worldwide have no effective DMARC protection, Business Email Compromise cost $2.7 billion in 2024 alone, and having a DMARC record doesn't mean you're actually protected.
The DMARC Reality Check:
Having It ≠ Being Protected
Here's what nobody tells you about DMARC:
most companies that have it aren't using it correctly.
Recent analysis of 859,048 domains worldwide reveals the uncomfortable truth:
71% have no effective DMARC protection
Only 10.7% have full protection (p=reject policy at 100% enforcement)
18.4% have partial coverage (quarantine or gradual rollout)
Translation: 94% of domains are spoofable.
But here's where it gets worse. When we look at domains that have DMARC records, over 80% use a policy of p=none—which means they're monitoring impersonation attempts but not actually blocking them.
Think about that. You deployed DMARC. You see it in your DNS records. You get reports. You feel protected.
You're not.
p=none is a security camera with no alarm. You'll have great footage of the robbery, but the money's still gone.
What DMARC Actually Is (The 60-Second Version)
DMARC (Domain-based Message Authentication, Reporting, and Conformance) is email's version of showing ID at the door.
Without it, anyone can send email claiming to be from your domain. With it, email receivers can verify the sender is legitimate and reject imposters.
DMARC has three policy levels:
p=none (Monitor Only):
"Tell me when someone impersonates me, but don't stop them"
You get reports showing spoofing attempts
Attackers' emails still reach their targets
This is where 80%+ of DMARC-enabled domains are stuck
p=quarantine (Partial Protection):
"Treat suspicious emails with caution"
Receiver-dependent behavior: most place emails in spam/junk folders; some major providers treat quarantine identically to reject
Better than p=none, but messages may still be accessible to recipients in spam folders
Not full protection
p=reject (Full Protection):
"Block impersonation attempts entirely"
Only 10.7% of domains worldwide use this
This is the only setting that actually protects you
Here's the kicker: DMARC has existed since 2012. We've had fourteen years to get this right. And we're still failing spectacularly.
The Attacker's Shopping List: How They Find You
Attackers don't guess. They scan.
Here's what they look for when targeting domains for Business Email Compromise attacks:
Step 1: The Domain Scan
Attackers use automated tools to check your DMARC status. It takes seconds.
They query your DNS records and see one of four things:
No DMARC record → Easy target, add to list
DMARC p=none → Easy target, add to list (you're just watching, not stopping)
DMARC p=quarantine → Harder, but possible
DMARC p=reject → Skip, move to next target
71% of domains fall into categories 1 and 2. You're basically holding up a sign that says "Spoofable Domain Here."
Step 2: The Attack
Once they've identified your domain as vulnerable, attackers have options:
Direct Domain Spoofing: Without DMARC enforcement, they can send emails that appear to come directly from yourcompany.com. The "From" address is real. Your logo is there. Your email signature is copied. Everything looks legitimate.
Display Name Spoofing: They register a lookalike domain (yourcompany-secure.com, yourcornpany.com) and set the display name to "John Smith, CFO" from your actual company. This technique appears in 36% of BEC emails.
Compromised Accounts: Sometimes they don't spoof at all—they just steal credentials and use real accounts. But when they DO spoof, DMARC is your only defense.
Step 3: The Payout
The average BEC incident costs $75,000 to $137,000. In the financial sector, median losses hit $125,000 per incident.
The largest single BEC scam? $121 million stolen from Facebook and Google combined.
In 2024 alone, BEC attacks cost $2.7 billion. Over the past decade? $55.5 billion.
And 73% of all reported cyber incidents in 2024 were BEC attacks.
Your unprotected domain isn't just vulnerable. It's actively being used as a weapon—against your customers, your partners, and your own employees.
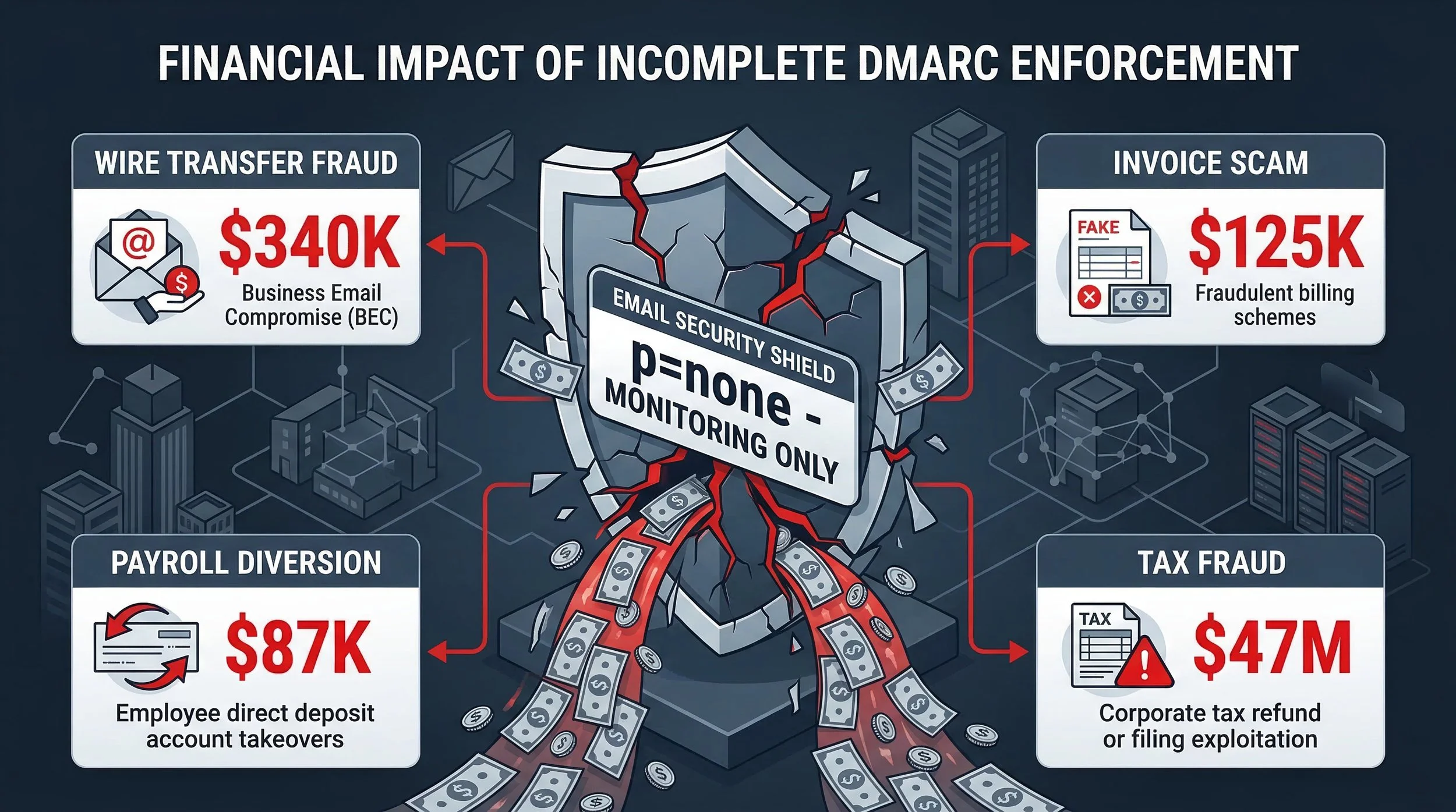
Real-World Impact: When DMARC Absence Becomes Disaster
The UK Tax Scam: £47 Million Gone
The attack worked because recipients trusted emails appearing to come from official government domains. Many of those domains lacked proper DMARC enforcement.
The Home Office Sponsorship Scam
Between July and August 2025, a sophisticated campaign impersonated the UK Home Office, targeting organizations with sponsor licenses. Attackers attempted to steal access to the Sponsorship Management System through spoofed official communications.
The scam succeeded because the emails looked legitimate—right domain, right formatting, right language.
Transport for London: The Infrastructure Attack
In 2024, a cyber attack on Transport for London compromised financial data for 5,000 customers. Attackers used spoofed "Critical Equipment Alerts" and fake manifests to bridge the gap between corporate inboxes and physical logistics systems.
The UK transport sector? Over 26% of domains lack DMARC entirely.
Higher Education: The Research Theft
91% of UK universities experienced a cyber breach in 2025. Yet only 23.9% enforce DMARC policies.
Attackers forge university login pages, gaining access to multi-million-pound research databases and student financial records. Email spoofing is the entry point.
Payment Fraud: The Silent Billions
In the first half of 2025 alone, payment fraud and scams stole over £629.3 million in the UK, often initiated by manipulated email communications.
Most victims had email security. What they didn't have was DMARC enforcement.
The False Security Trap: Why Companies Get Stuck at "Monitor"
Here's the dirty secret about DMARC: deployment is easy. Enforcement is terrifying.
And that's why 508,269 domains use monitoring-only policies while only 350,513 actually enforce protection.
The XML Report Problem
You deploy DMARC with a p=none policy. Congratulations—you're monitoring!
Now you get dozens of XML reports daily from Gmail, Microsoft, Yahoo, and other email providers. High-volume senders can receive 40+ reports per day; even smaller organizations typically get 5-10 daily.
Each report contains cryptographic data about who's sending email claiming to be you. Can you parse XML? Can you correlate data across hundreds of reports? Can you identify which "failures" are legitimate (your marketing platform) versus malicious (attackers)?
No?
Neither can 99% of IT teams.
This is why companies deploy DMARC and never move past p=none. The reports are incomprehensible. The volume is overwhelming. The fear of breaking legitimate email is paralyzing.
So they just... leave it. Forever.
They tell themselves they're "monitoring the situation." What they're actually doing is watching themselves get robbed in high definition.
The Fear of Breaking Email
Here's what keeps IT teams awake at night:
"What if we move to p=reject and accidentally block our CEO's emails?"
"What if our CRM can't authenticate properly and all our sales emails get rejected?"
"What if that third-party billing system we set up three years ago stops working?"
These aren't irrational fears. They're legitimate concerns.
But here's the uncomfortable truth: attackers are counting on your fear.
Every day you stay at p=none is another day they can impersonate your domain with impunity.
The Business Case: What DMARC Enforcement Actually Stops
Let's talk numbers.
The Attack Volume
BEC attacks increased 15% in 2025 compared to 2024. One security firm intercepted over 3,000 BEC messages per month on average, with peaks hitting 4,300 in July.
63% of organizations experienced BEC in 2024.
This isn't theoretical. This is constant, industrial-scale targeting.
The Financial Impact
BEC attacks cost an average of $4.89 million per breach—making them the second most expensive type of breach after ransomware.
The average wire transfer request in early 2025 was $24,586. 64% of victims lost more than $10,000.
For some organizations, a single successful BEC attack is existential.
The Policy Impact: Proof That Enforcement Works
Here's the data that should end all debate:
Meanwhile, countries without enforcement mandates—like the Netherlands—saw vulnerability increase to 97%.
DMARC enforcement works. The data is unambiguous.
The question isn't whether it's effective. The question is whether you'll implement it before or after you get hit.
The Compliance Mandate: DMARC Is No Longer Optional
If the financial risk and security benefits aren't enough, here's the regulatory reality:
PCI DSS v4.0 (Effective March 31, 2025)
Non-compliance can result in penalties ranging from $5,000 to $100,000 per month, depending on severity and duration of the violation.
p=none doesn't count. You must enforce.
Email Provider Requirements
Google, Yahoo, and Microsoft have all implemented sender requirements mandating DMARC for high-volume senders. While p=none technically satisfies their requirements, it provides zero security benefit.
You're checking a compliance box while leaving your domain wide open to abuse.
Cyber Insurance
Insurers are increasingly asking: "Do you have DMARC enforced?"
Notice the word: enforced. Not "Do you have a DMARC record?" Not "Are you monitoring?"
Enforced means p=quarantine or p=reject.
Without it, expect higher premiums—or denied coverage entirely.
What DMARC Monitoring Services Actually Do (And Why You Need One)
Remember that XML report problem? This is where monitoring services earn their keep.
The Translation Layer: From Chaos to Clarity
A DMARC monitoring platform like Red Sift takes those 47 daily XML reports and translates them into actionable intelligence:
WHO is sending email from your domain:
Your legitimate services (CRM, marketing, HR systems)
Third-party vendors
Attackers actively spoofing your domain
WHERE they're sending from:
Geographic analysis
IP address tracking
ISP identification
WHAT percentage is passing/failing authentication:
Real-time compliance metrics
Trend analysis over time
Failure categorization
WHEN impersonation attempts spike:
Temporal pattern recognition
Attack campaign identification
Seasonal variations
WHY emails are failing authentication:
Misconfigured SPF records
Missing DKIM signatures
Alignment issues
Specific fix instructions
Instead of XML gibberish, you get: "Your marketing platform is misconfigured. Here's how to fix it." Or: "Someone in Nigeria is actively spoofing your CFO. Here's the evidence."
The Discovery Process: Finding Your Legitimate Senders
Here's the problem nobody talks about: you don't actually know everyone who sends email on your behalf.
You know about your CRM (Salesforce, HubSpot). You know about your marketing platform (Mailchimp). You probably know about your HR system.
But what about:
The contractor who set up that automated report three years ago?
The third-party payroll processor?
The customer support platform?
The billing system?
The event registration service?
That SaaS tool the sales team started using last quarter?
DMARC monitoring discovers all of them.
Red Sift and similar platforms show you: "These 47 sources are sending email as you. 23 are authenticated properly. 24 are not. Here's how to fix the 24."
Without this visibility, moving from p=none to p=reject is terrifying. You could break legitimate email and never know which service failed until customers complain.
With this visibility, it's a roadmap.
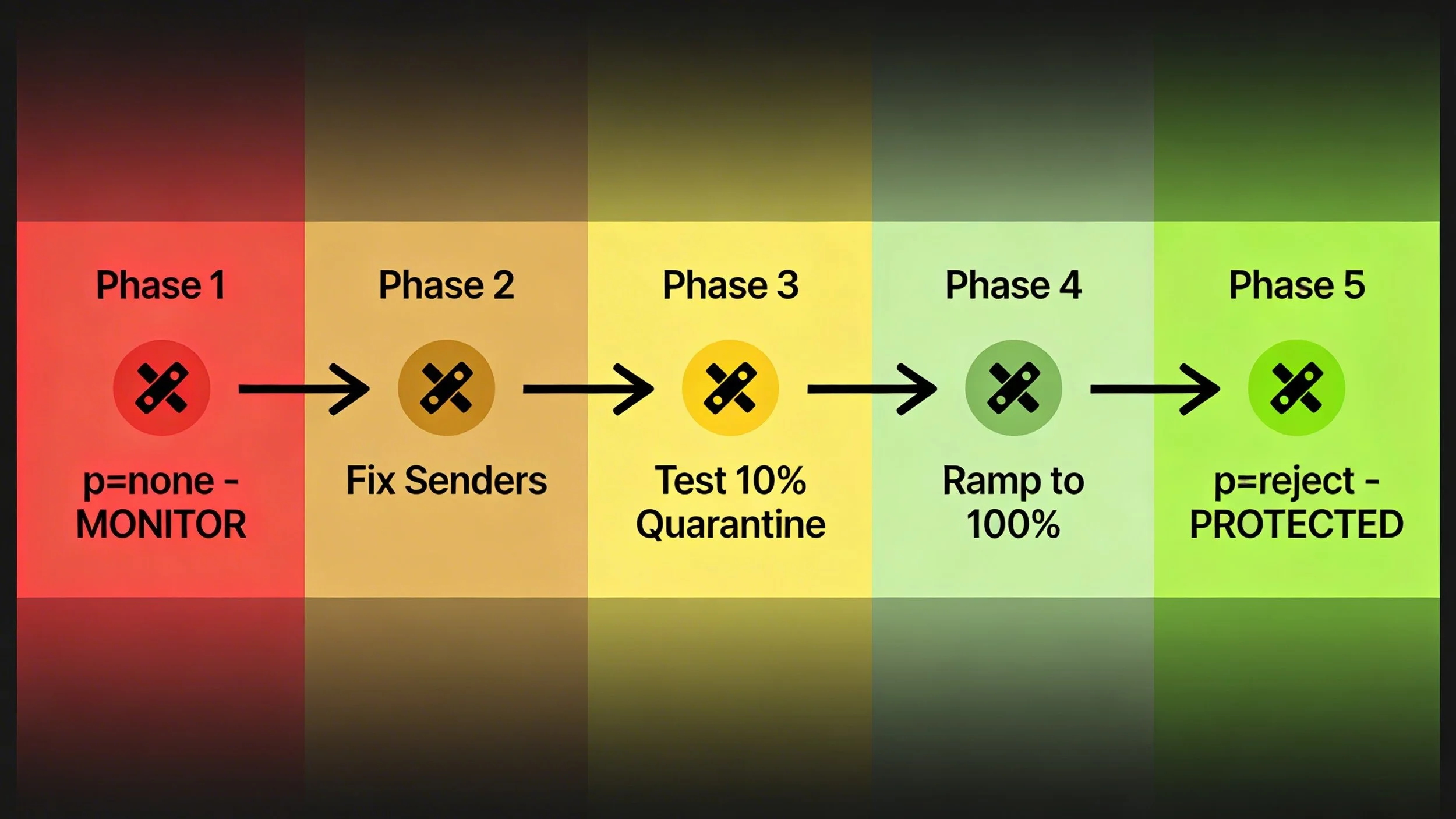
The Enforcement Path: From Monitoring to Protection
The monitoring service doesn't just show you data—it guides you to actual protection.
Phase 1: Deploy p=none
Start monitoring
Collect 2-4 weeks of data
Discover all email sources
Phase 2: Fix Legitimate Senders
Service identifies misconfigured sources
Provides specific fix instructions
Verify fixes in real-time
Phase 3: Move to p=quarantine at 10%
Test enforcement with small percentage
Monitor for issues
Service tells you if anything breaks
Phase 4: Ramp to 100% Quarantine
Gradually increase percentage
Continuous monitoring
Address issues as they arise
Phase 5: Move to p=reject
Full enforcement
Complete protection
Ongoing monitoring for new senders
Without monitoring: You're stuck at Phase 1 forever — With monitoring: You reach Phase 5 in weeks, not years.
The Threat Intelligence Bonus:
When you do get attacked (and you will), the monitoring service provides:
Attacker's IP addresses
Geographic origin
Volume of spoofing attempts
Target recipient addresses
Email content patterns
Timeline of attack campaign
You can:
Block the IPs at your gateway
Alert customers to the threat
File reports with law enforcement
Provide evidence to cyber insurance
Understand attack patterns
It's not just protection—it's attribution and evidence.
The Compliance Proof
Cyber insurance renewal? Compliance audit? Customer security questionnaire?
With a monitoring service:
Generate compliance reports instantly
Prove p=reject enforcement with data
Demonstrate ongoing monitoring
Show threat detection and response
Without it:
"Uh, we have DMARC... I think?"
No proof of enforcement
No visibility into threats
Premium goes up or coverage drops
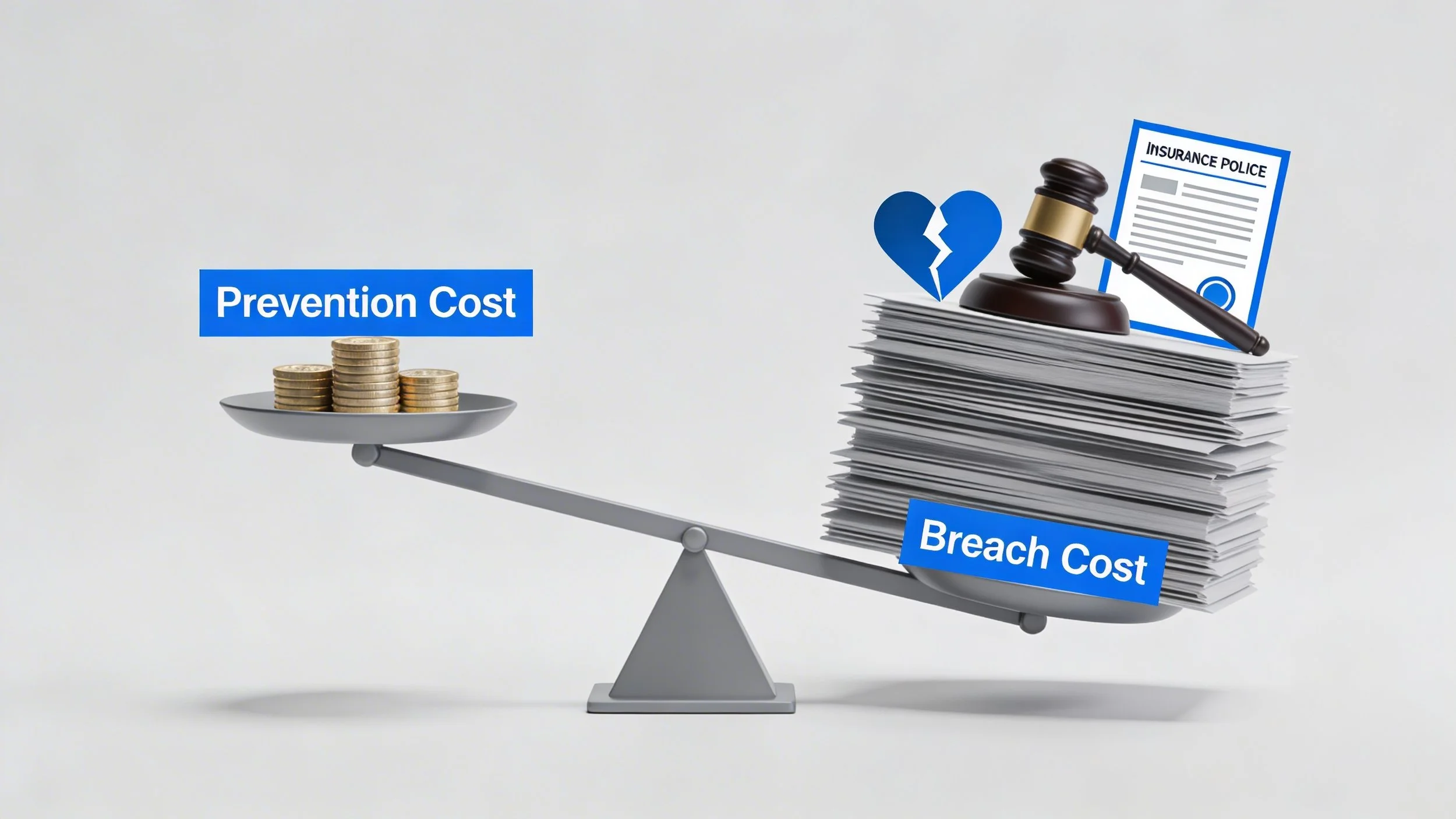
The ROI: Prevention vs. Reaction
Let's do the math.
The Cost of DMARC Monitoring:
Red Sift pricing varies by domain count and email volume, but for most mid-sized organizations, expect:
Setup: One-time implementation
Monthly service: Ongoing monitoring, reporting, support
Time to enforcement: 4-12 weeks
Total investment: Thousands annually.
The Cost of Not Having It:
Average BEC incident: $75,000 - $137,000
Average breach (all causes): $4.89 million
Financial sector median BEC loss: $125,000 per incident
Plus:
Legal fees
Forensic investigation
Customer notification
Credit monitoring services
Regulatory fines
Reputational damage
Lost business
Insurance premium increases
One successful BEC attack pays for decades of DMARC monitoring.
The Opportunity Cost of p=none:
Every day you stay at p=none, you're:
Watching attacks happen
Collecting evidence of your vulnerability
Gaining zero protection
Remaining spoofable
You're paying for monitoring that provides no security benefit.
That's not ROI. That's waste.
How to Check Your Domain Right Now
Want to know if you're protected? Here's the 60-second audit:
Step 1: Check Your DMARC Record
Open a terminal or command prompt and run:
nslookup -type=txt _dmarc.yourdomain.com
Or use an online tool like:
https://mxtoolbox.com/dmarc.aspx
https://dmarcian.com/dmarc-inspector/
Step 2: Interpret the Results
No DMARC record found:
You have zero protection
Your domain is completely spoofable
Immediate action required
DMARC record exists with "p=none":
You're monitoring only
Zero protection from spoofing
You need to move to enforcement
DMARC record exists with "p=quarantine":
Partial protection (receiver-dependent)
Most receivers quarantine to spam; some treat as reject
Should move to p=reject for guaranteed blocking
DMARC record exists with "p=reject":
Full protection (if at 100%)
Verify pct=100 or no pct tag
Confirm RUA reporting is set up
Step 3: Take Action Based on Results
If you have no DMARC:
Start with p=none immediately
Set up reporting (RUA tag)
Monitor for 2-4 weeks
Engage DMARC monitoring service
Move to enforcement
If you have p=none:
How long have you been monitoring? (If >3 months, you're stuck)
Do you understand your reports? (Probably not)
Engage monitoring service to move to enforcement
Don't stay here forever
If you have p=quarantine or p=reject:
Verify percentage (pct tag)
Confirm reporting is active
Consider monitoring service for ongoing visibility
Good job—you're in the 10.7%
The THINKFLEX Approach
Email Impersonation Protection
THINKFLEX provides comprehensive Email Impersonation Protection powered by Proofpoint and Red Sift DMARC management.
Our approach addresses the complete DMARC lifecycle:
Assessment
We audit your current DMARC status and identify gaps:
Current policy level
Reporting configuration
SPF and DKIM alignment
Legitimate sender inventory
Enforcement readiness
Implementation
We deploy DMARC with proper monitoring:
Configure p=none with reporting
Set up Red Sift monitoring platform
Establish baseline visibility
Identify all email sources
Remediation
We fix legitimate senders before enforcement:
Analyze authentication failures
Provide specific fix instructions
Verify corrections
Document all authorized senders
Enforcement
We move you to protection:
Gradual rollout (10% → 100%)
Continuous monitoring
Issue resolution
Full p=reject enforcement
Ongoing Management
We maintain protection over time:
Monitor for new senders
Detect spoofing attempts
Provide threat intelligence
Compliance reporting
Quarterly reviews
We don't just deploy DMARC. We get you to enforcement—and keep you there.
The Bottom Line: Your Domain Is Either Protecting You or Being Used Against You
There's no middle ground.
71% of domains have no DMARC protection. Another 18.4% have partial coverage. Only 10.7% are fully protected.
That means 94% of domains can be spoofed.
Business Email Compromise cost $2.7 billion in 2024. $55.5 billion over the past decade. 73% of all cyber incidents are BEC.
Your unprotected domain isn't just vulnerable—it's actively being weaponized. Against your customers. Against your partners. Against your own employees.
Having DMARC isn't enough. Having it set to p=none is security theater.
You're monitoring yourself get robbed in 4K. You're collecting evidence of your own vulnerability. You're paying for the privilege of watching attackers impersonate your brand.
Enforcement is the only thing that matters.
And enforcement requires visibility, guidance, and ongoing management—which is exactly what DMARC monitoring services provide.
The data is clear. The threat is real. The solution exists.
The only question is: Will you implement it before or after you become a statistic?
Take Action: Check Your DMARC Status Now
Step 1: Run a DMARC check on your domain (see instructions above)
Step 2: If you have no DMARC or p=none, understand you're currently unprotected
Step 3: Contact THINKFLEX to discuss Email Impersonation Protection
We'll audit your domain, identify gaps, and provide a roadmap to full DMARC enforcement with Red Sift monitoring.
Because in 2026, p=none is not a security strategy.
It's a confession.
Ready to move from monitoring to protection? Contact THINKFLEX to discuss Email Impersonation Protection powered by Proofpoint and Red Sift DMARC management.
Sources and Further Reading
DmarcDkim.com Global Adoption Statistics (February 2026) - 859,048 domains monitored, 71% unprotected - Source
EasyDMARC 2025 DMARC Adoption Report - Enforcement vs. monitoring gap, US policy impact - Source
PowerDMARC Email Phishing and DMARC Statistics 2026 - 10 million domain analysis, 18% adoption - Source
Red Sift Global DMARC Adoption Guide (January 2026) - 73.3 million domains, 14.9% adoption, public company analysis - Source
PowerDMARC UK DMARC & MTA-STS Report (February 2026) - UK sector analysis, case studies - Source
FBI IC3: Business Email Compromise - The $55 Billion Scam - BEC losses 2013-2023 - Source
LevelBlue SpiderLabs: BEC Email Trends 2025 - 15% increase, $2.7B in 2024 - Source
Hoxhunt: Business Email Compromise Statistics 2026 - BEC trends, AI-generated attacks, 73% of incidents - Source
Nacha: FBI IC3 Finds $8.5 Billion Lost to BEC - 3-year losses, 63% of orgs hit - Source
Gitnux: Business Email Compromise Statistics - Average costs, incident data - Source
Valimail: 2026 State of DMARC Report - Policy analysis, industry trends - Source