Strong Protection.
Strong Leadership.

Protect your business with trusted cybersecurity solutions and senior-level IT leadership.
Built on trusted platforms.
Backed by experienced, security-first governance.

We help businesses close gaps, reduce risk, and bring structure to protection across people, systems, and strategy.
THINKFLEX Delivers
Cyber Protection
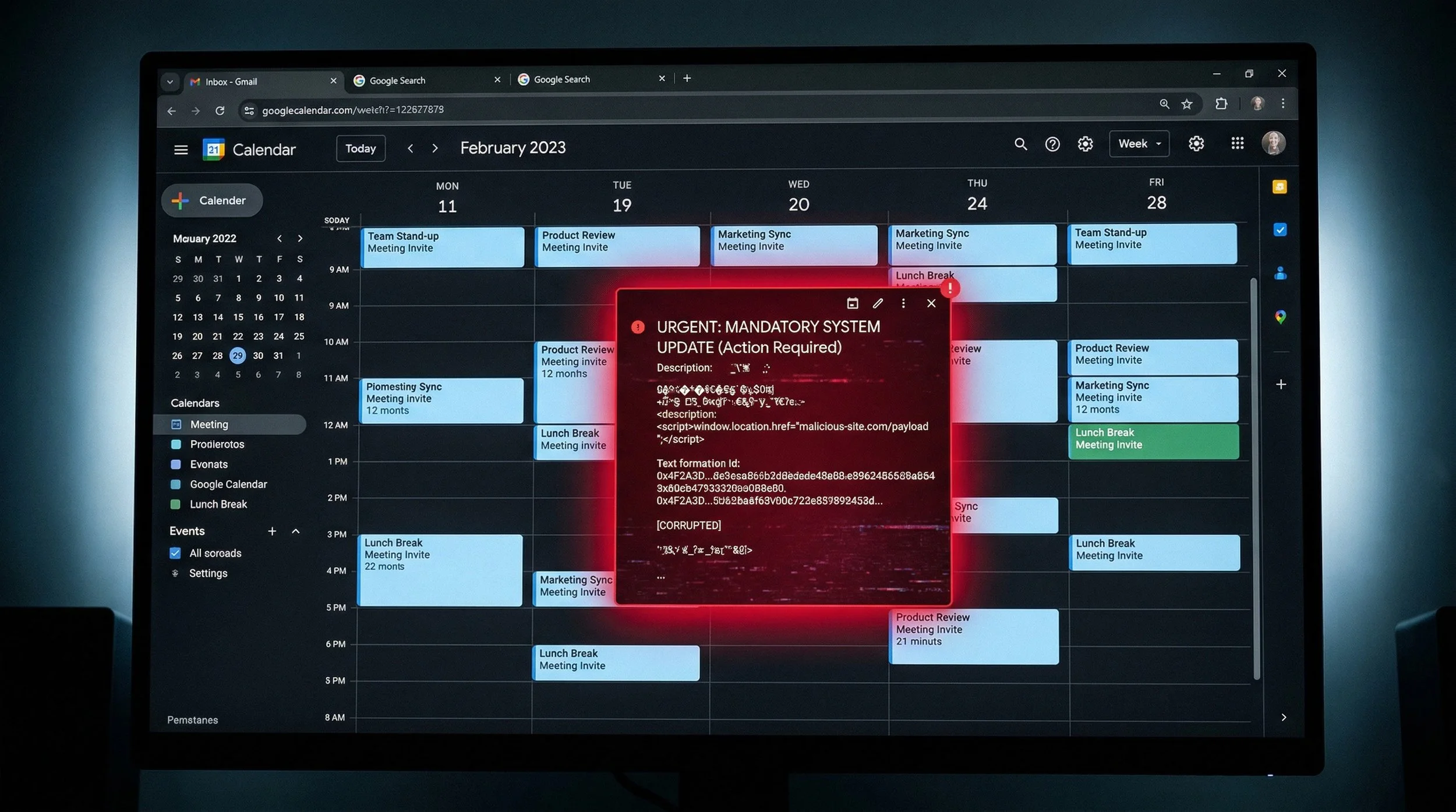
Secure email, endpoints, mobile devices, backups, identity, and business-critical systems with layered protection designed for real-world threats.
Protect what attackers target first
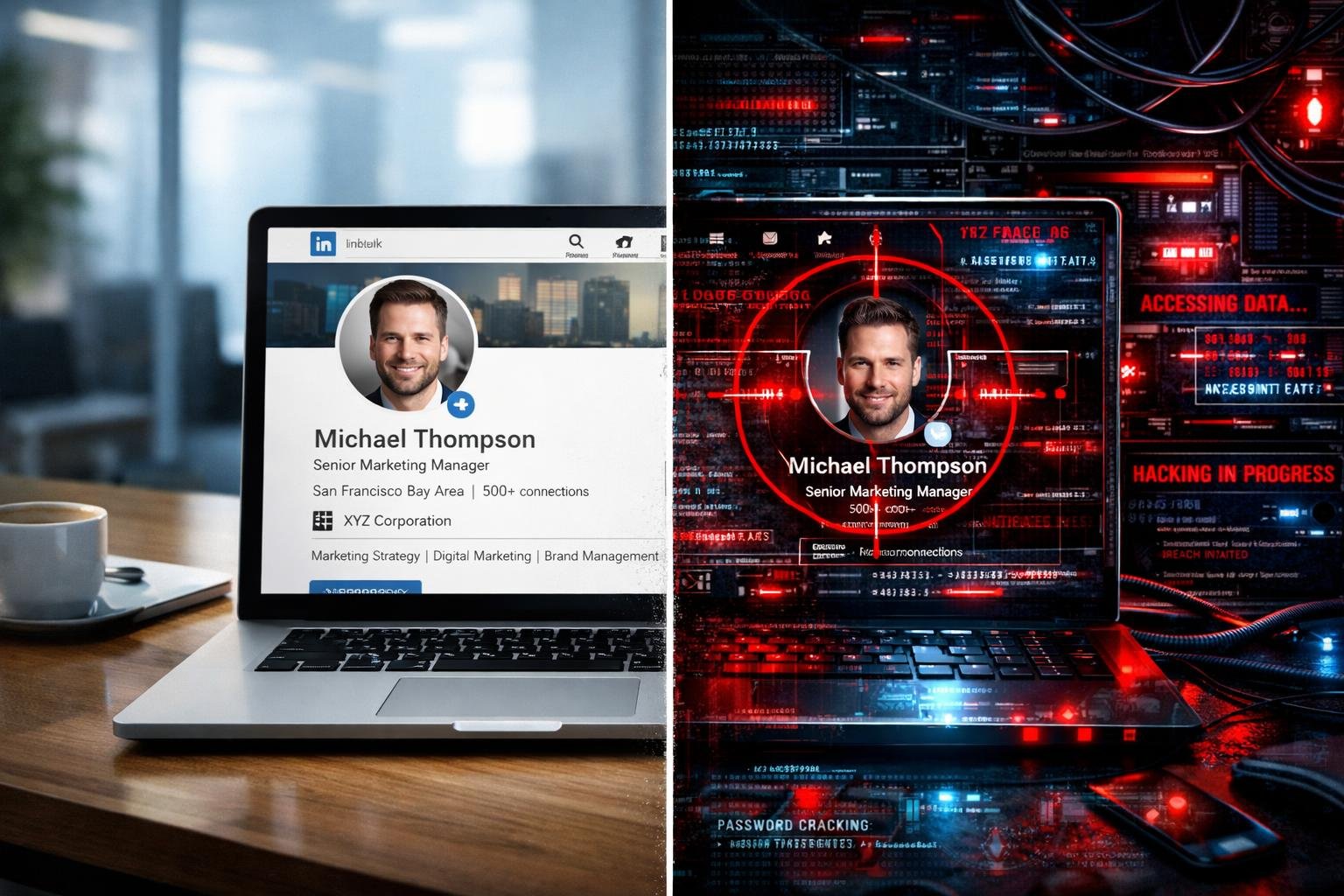
Security Training
Help staff recognize phishing, impersonation, and modern social engineering attacks through practical, ongoing security awareness training.
Reduce user risk through awareness
Technology Leadership
Get senior-level cybersecurity and IT guidance
Align security and IT decisions with business priorities through strategic advisory, vCIO support, and practical risk-based planning.
Start With a Complimentary
Cyber Exposure Snapshot

A clear picture of your security posture in four critical areas:
Email Authentication - We verify your domain's email protection is actively blocking imposters, not just monitoring them. You'll know if scammers can send fake emails claiming to be from your staff.
Breached Credentials - We scan public breach databases to identify which employee accounts have been compromised. You'll see exactly who's at risk and what data was exposed.
Web Security - We check if your website has the standard security features modern browsers need to protect visitors. You'll understand what's missing and how it affects people accessing your services.
AODA Accessibility - We assess your site's compliance and usability for residents with disabilities. You'll get a score out of 10 and know what needs fixing to maintain accessibility standards.
Each finding comes with:
What we found (in plain language)
What it means for your organization
How THINKFLEX fixes it
No overwhelming technical jargon. No expensive ongoing commitments. Just a clear snapshot of where you stand and a roadmap to fix what matters most.
Why Businesses Choose
THINKFLEX

You don’t need more noise, more dashboards, or more disconnected tools.
You need practical cybersecurity leadership, protection that fits your business, and a partner who understands how risk, operations, and IT all connect.
Security-first approach across email, endpoints, mobile, backups, identity, and user risk
Strategic guidance built in with vCIO and advisory support available where needed
Flexible delivery model that works alongside internal teams or fills the gap where no internal team exists
Trusted solutions without enterprise overhead so protection scales without unnecessary complexity
Business-minded communication that keeps security clear, relevant, and actionable
Focused on the Risks
That Impact Businesses Every Day
Built to Support Organizations of
Any Size

THINKFLEX provides practical cybersecurity solutions and experienced IT leadership that scale to fit your needs. From a single service to broader strategic support, we help protect organizations of any size.
Whether you need a single service, broader cyber protection, or senior-level IT and cybersecurity leadership, THINKFLEX can work alongside your existing team or support you directly
Individual users and small businesses
Growing organizations
Mid-sized and enterprise environments
Teams needing targeted support or broader strategic guidance
Technology Insights for Modern Business
Explore real-world guidance on phishing, impersonation, mobile threats, insider risk, cyber readiness, and the security issues businesses are dealing with now.