Your LinkedIn Profile Is Worth $50,000 to Hackers. What's It Worth to You?
Your LinkedIn profile tells a story. Your name, your company, your role as VP of Finance. Your direct reports. When you're traveling for that conference in Miami next week. Your communication style from the articles you've posted. Your hometown (security question answer). Your previous employers (more security questions). Your MBA from State University (another security question). Your professional network of 500+ connections showing exactly who reports to whom.
To you, it's professional networking. Career opportunities. Business connections.
To hackers, it's a complete attack blueprint worth an average of $125,000 USD per successful Business Email Compromise.
And your profile is just one of 4.3 billion professional records exposed in November 2025 alone, enriched with 429 billion correlated attributes linking your home address, phone number, and personal information directly to your high-value corporate email.
Welcome to 2026, where your professional identity is being weaponized at industrial scale, and the question isn't whether you'll be targeted—it's whether you'll survive the hit.
The Professional Identity Goldmine
Here's what most people don't realize about LinkedIn data breaches: they're not random leaks. They're curated intelligence packages being actively enriched, correlated, and sold.
In November 2025, a 16-terabyte database containing 4.3 billion professional records was discovered publicly accessible online. It wasn't just scraped LinkedIn data—it was aggregated from multiple sources and enriched with an average of 429 billion attributes per identity.
What does that mean in practice?
Your LinkedIn profile shows:
Your full name and current employer
Your job title and responsibilities
Your professional connections (organizational chart)
Your communication style (from posts and articles)
Your travel schedule (conference posts)
Your interests and hobbies
Your education and hometown (security questions)
Your previous employers (more security questions)
The enriched database adds:
Your home address
Your personal phone number
Your family members (correlated from other sources)
Your email patterns
Your professional hierarchy
Your vendors and partners
Cross-references to other compromised accounts
The result? "Surgically precise, autonomous impersonation" across LinkedIn, WhatsApp, corporate email, and any other platform where your professional identity matters.
This isn't theoretical. In the ongoing LinkedIn scraping operations, 500 million profiles are being actively sold on dark web forums right now. Full names, email addresses, phone numbers, workplace information—all available to anyone willing to pay.
The Public and Education sectors saw a 569% increase in breach volume in 2025 vs 2024. Why? Because these platforms are "identity goldmines" linking personal information directly to high-value corporate and government email addresses.
Your professional identity isn't just exposed. It's being industrially processed for weaponization.
The $2.9 Billion Business Email Compromise Blueprint
Here's how your LinkedIn profile becomes a $125,000+ USD payday for attackers.
Business Email Compromise (BEC) caused $2.9 billion USD in losses in 2024-2025, making it the second-costliest cybercrime after investment scams. BEC accounts for 73% of all reported cyber incidents, and the average claim cost has more than doubled from $84,000 USD in 2022 to $183,000 USD in 2023.
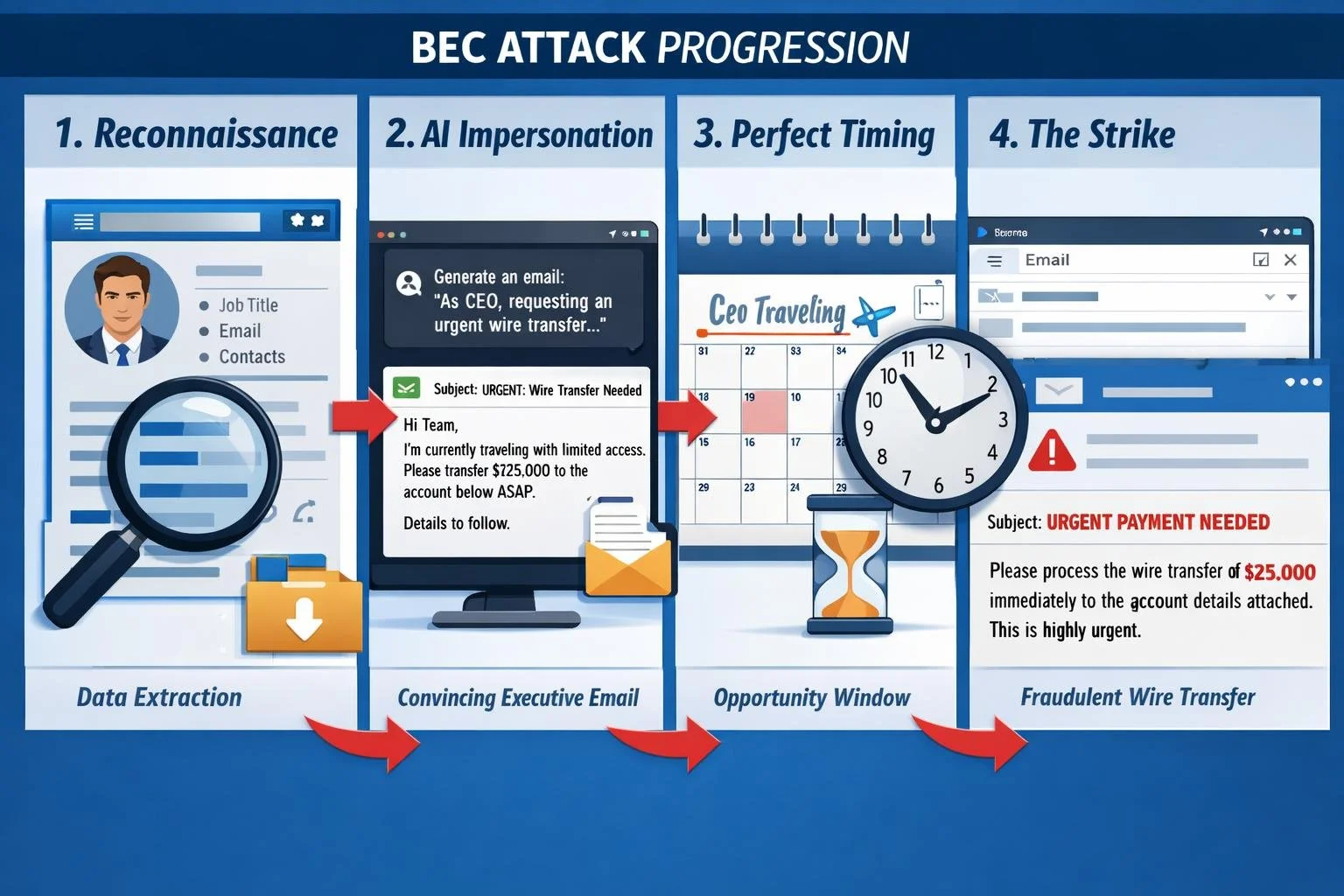
The blueprint is simple and devastatingly effective:
Step 1: LinkedIn Reconnaissance
85% of BEC campaigns involve studying target email structures and communication patterns before launching attacks. Attackers don't guess—they research.
They learn:
Who the CFO is (LinkedIn title search)
Who reports to the CFO (LinkedIn connections)
The CFO's communication style (LinkedIn posts and articles)
When the CFO is traveling (conference posts: "Great panel discussion at FinCon2026!")
The company's current initiatives (company page updates)
Email domain structure (from employee emails visible on profiles)
Step 2: AI-Powered Impersonation
By mid-2024, 40% of BEC emails were AI-generated. Attackers feed your LinkedIn content into AI tools that:
Mimic your writing style
Reference real projects and colleagues
Use appropriate urgency without obvious red flags
Generate grammatically perfect, contextually accurate emails
ChatGPT's free version can generate 30 phishing email templates per hour. The paid versions do it faster, better, and at scale.
Step 3: Perfect Timing
You post on LinkedIn: "Excited to speak at the Miami FinTech Summit next week!"
The attacker now knows:
You'll be distracted and traveling
You might be responding to emails quickly on mobile
You won't be at your desk to verify unusual requests
Your team knows you're out of office
Step 4: The Strike
An email arrives in your Accounts Payable manager's inbox. It appears to come from you (the CFO). The display name matches perfectly. The email signature is correct. The writing style sounds exactly like you.
"Quick question while I'm between sessions—can you process this wire transfer for the acquisition due diligence? Vendor needs payment today to release documents. Details attached. Thanks!"
60% of BEC attacks target employees OUTSIDE finance and executive roles precisely because they're less suspicious of urgent requests from leadership.
The Success Rate
BEC scams succeed 22% of the time. That's not a failure rate—that's a business model. When the average successful attack nets $125,000 to $183,000 USD, a 22% success rate is extraordinarily profitable.
And it gets worse: 36% of BEC emails simply alter the display name to impersonate executives. They don't even need to compromise your actual email account—they just need your LinkedIn data and basic email spoofing.
The Personal Identity Cascade: When LinkedIn Leads to Everything
Let's say you're not a CFO. You're just a professional with a LinkedIn profile. Maybe you think you're not a high-value target.
You're wrong.
In Canada,Canadians lost $638 million CAD to fraud in 2024, with 34,621 reported victims. Identity fraud was the most reported type.
In the United States,over 1.1 million Americans filed identity theft complaints in 2024, a 9.5% increase from 2023.
Across North America, one in four people has been a victim of identity theft, and 30% had their identity stolen in the past year alone.
Here's how your LinkedIn profile becomes the first domino:
The Credential Reuse Problem
Your LinkedIn email is jsmith@company.com. You also use that email for:
Your personal Gmail
Your online banking
Your cloud storage
Your social media accounts
Your work VPN access
The 2026 Identity Breach Report found that 68.89% of all breached passwords now arrive in plaintext—a 261% year-over-year increase. Why? Because infostealer malware scrapes passwords directly from your browser memory before they're even hashed, rendering server-side security completely irrelevant.
Over 94 billion credentials and cookies were exposed in just two years. Your email from LinkedIn + your password from that old Adobe breach + credential stuffing automation = access to everything.
The Session Hijacking Bypass
"But I use multi-factor authentication!"
Doesn't matter. Modern infostealer malware captures active session cookies, allowing attackers to clone your active login state and bypass MFA entirely by inheriting your "trusted device" status.
In 2025, 51.7 million infostealer packages were processed (up 72% year-over-year), identifying 24.8 million unique infected devices. If your device is compromised, your active sessions—MFA and all—are compromised.
The Financial Devastation
In the United States:The average identity theft victim loses $7,600 USD. That's the average. The reality is far worse:
37% of victims lose $10,000 USD or more
22% of victims lose $100,000 USD or more
3% of victims lose $1 million USD or more
Total identity fraud and scam losses hit $43-47 billion USD in 2024.
In Canada: While specific average loss data varies, Canadian victims lost $638 million CAD collectively in 2024, and only 5-10% of fraud is actually reported, meaning the real impact is far higher.
But the financial loss is just the beginning.
The Emotional Toll
16% of identity fraud victims contemplated suicide due to the stress—up from just 2-3% twenty-five years ago. 43% experienced anxiety or depression, 42% developed trust issues, and 33% feel constantly fearful of future scams.
60% of victims required several weeks to regain control of their identity. Another 20% required several months.
The Repeat Victimization Cycle
It doesn't end with one attack. 31.5% of victims were victimized twice in the past year, and 24.6% were hit three times.
Once you're in the system as a confirmed victim who responds to attacks, you become a permanent target.
The Small Business Death Sentence
If you're a small business owner reading this and thinking "we can't afford comprehensive cybersecurity," you need to understand the math.
In the United States: 60% of small businesses are forced to shut down within six months of a major cyber breach.
In Canada: 16% of Canadian businesses were impacted by cybersecurity incidents in 2023, and spending on recovery doubled to $1.2 billion CAD from 2021 to 2023.
Not "experience financial hardship." Not "face challenges." Many shut down permanently.
You're the Primary Target
Small and medium-sized businesses are targeted four times more often than large enterprises in 2025. Why? Because:
You have valuable data (customer information, financial records, intellectual property)
You have access to larger companies (supply chain attacks)
You have far weaker defenses than enterprises
You're less likely to have cyber insurance
You're more likely to pay ransoms to survive
In Canada:Over 85% of Canadian companies were affected by successful cyberattacks in one year, and almost two-thirds expect to be hit with ransomware.
You're Managing Security Without Training
84% of business owners self-manage their cybersecurity, and 54% of those with a dedicated cyber expert still manage the program themselves.
The kicker? 28% admit the person managing cybersecurity doesn't have sufficient training—and most often, that person is the business owner.
You're defending against professional attackers using AI-powered tools, industrial-scale credential databases, and billion-dollar criminal infrastructure... with Google searches and hope.
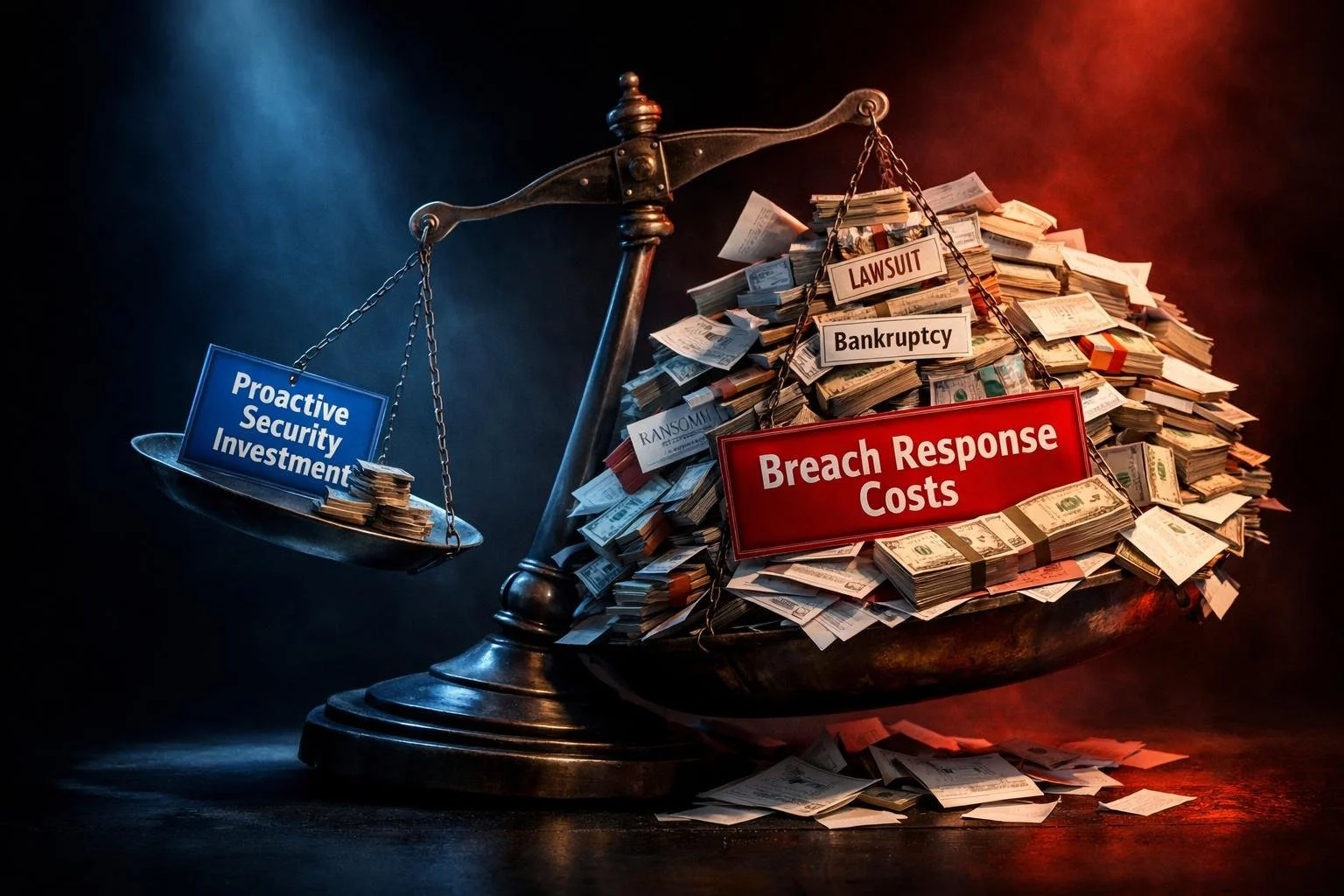
The False Economy: Coffee vs. Cybersecurity
Here's the uncomfortable truth that most business owners don't want to face:
Many North American businesses spend more on:
Office coffee and snacks
Software licenses they barely use
Monthly subscriptions they forgot about
Than they would on email security, endpoint protection, or backup solutions.
"We can't afford cybersecurity" really means "We haven't made it a priority."
Because when the breach happens, you'll suddenly find money for:
$1.47 million USD average in detection and escalation costs
$50,000-$500,000 USD (estimated) in legal fees
$100+ per customer for breach notification
Potentially millions in ransom demands
Proactive security investments are ordinary business expenses, typically tax-deductible in both the U.S. and Canada. Breach response costs are catastrophic losses that threaten your existence.
One protects your business. The other buries it.
(Consult your tax professional for guidance specific to your situation.)
The North American Breach Cost Reality
United States:The average breach cost is $10.22 million USD—an all-time high for any region, up 9% from 2024.
Canada:The average breach cost is $6.98 million CAD ($5.2 million USD equivalent), up 10.4% from 2024, bucking the global trend of declining breach costs.
"But we're a small business, not a Fortune 500!"
Doesn't matter. Here's how costs break down for smaller organizations:
Detection and Escalation:$1.47 million USD average—the highest cost component. This is just figuring out what happened and containing it.
Forensic Investigation: Estimated $20,000-$100,000+ USD to determine breach scope, identify compromised systems, and collect evidence.
Legal Counsel: Estimated $50,000-$500,000+ USD depending on breach scope, regulatory implications, and potential lawsuits.
Customer Notification:$100+ USD per affected individual. If you breach 1,000 customer records, that's $100,000 just in notification costs.
Credit Monitoring: Ongoing per-person costs that add up fast.
Regulatory Fines:33% of breached organizations face regulatory fines, and only 8% paid less than $25,000 USD.
Business Interruption: The average organization takes 241 days to identify and contain a breach. That's eight months of disruption, lost productivity, and potentially lost revenue.
Ransomware (if applicable):Average ransomware incident costs $1.85 million USD, with average ransom demands now at $2 million USD (a 500% increase in one year).
Add it up, and even a "small" breach can easily exceed $500,000 to $2 million USD for an SMB.
Most small businesses don't have that kind of cash. Hence: 60% close within six months.
The Reactive Tax: Why "We'll Deal With It If It Happens" Costs 100x More
Let's talk about the penny-wise, pound-foolish trap that kills businesses.
Organizations skip proactive security because they see it as an expense. Security awareness training? Expense. Email protection? Expense. Endpoint detection? Expense. Backup and disaster recovery? Expense.
Then they get breached and discover that "dealing with it if it happens" costs 10 to 100 times more than prevention would have.
The Time Factor
On average, hackers retain access to compromised systems for nearly six months before detection.
Six. Months.
During that time, they:
Map your entire network
Identify your most valuable data
Exfiltrate financial records, customer information, intellectual property
Establish persistent backdoors
Study your backup systems to ensure they can encrypt those too
Wait for the perfect moment to deploy ransomware
Every day they have access, the damage compounds. The cost multiplies.
The Detection Gap
Organizations without AI and automation take an average of 284 days to identify and contain a breach.
Organizations WITH extensive AI and automation do it in 204 days—80 days faster.
80 days is 11 weeks. That's nearly three months of additional data theft, system compromise, and escalating damage.
The cost savings from using AI and automation? Nearly $1.9 million USD compared to organizations without these tools.
In Canada specifically:Organizations using extensive security AI report average breach costs of $5.19 million CAD vs. $8.53 million CAD for those not using these tools—a $3.34 million CAD difference.
The Human Element
60% of breaches involve the human element—error, privilege misuse, stolen credentials, or social engineering.
22% of breaches start with stolen credentials, making credential abuse the #1 attack vector. And credential theft is up 71% year-over-year.
Want to know why? Because only 6% of passwords are completely unique. People reuse passwords across personal and work accounts, making credential stuffing attacks trivially easy.
The median time for a user to fall for a phishing email? Less than 60 seconds.
You can have the best technical defenses in the world, but if your people click malicious links, use weak passwords, and don't recognize social engineering, you're one email away from disaster.
The Penny-Wise, Pound-Foolish Trap
Organizations say they "can't afford" proactive security to "save money," then discover:
They "couldn't afford" thousands per month in proactive security
But they CAN afford $1.47 million USD in breach response
They CAN afford $500,000+ USD in ransom payments
They CAN afford to close the business permanently
It's not about affording security. It's about priorities. And priorities have a way of clarifying themselves—usually when it's too late.
The Cost Multiplier in Action
Scenario: Small Business Skips Security
Skips email security platform
Skips endpoint detection and response
Skips security awareness training
Skips immutable backup solution
Skips incident response planning
Annual "savings": Thousands in avoided security costs.
Then: Ransomware Attack
Ransomware deployed via phishing email (no email security to block it)
Spreads across all endpoints (no EDR to detect and contain)
Employees don't recognize the attack (no security training)
Backups encrypted along with production systems (no immutable backups)
No incident response plan—chaos and confusion
Actual costs:
Forensic investigation: $50,000 USD
Legal counsel: $100,000 USD
Ransom payment (business decides to pay): $500,000 USD
Lost revenue during 3-week shutdown: $300,000 USD
Customer notification (5,000 customers): $500,000 USD
Credit monitoring services: $150,000 USD
Regulatory fines: $100,000 USD
Lost customers and contracts: $2 million+ USD
Total impact: $3.7+ million USD
Time to close business: 4 months
Scenario: Business Invests in Prevention
The same business instead implements proactive security:
Email security (blocks phishing before it reaches inboxes)
Endpoint detection and response (catches malware immediately)
Security awareness training (employees recognize and report phishing)
Immutable backup solution (recovery without paying ransom)
Incident response plan (coordinated response, faster recovery)
Multi-factor authentication (blocks credential theft)
Annual investment: Thousands in proactive security (typically tax-deductible as ordinary business expenses).
Then: Attack Attempted
Phishing email blocked by email security
Malware detected and quarantined by EDR
Employee recognizes suspicious email and reports it
MFA blocks credential stuffing attempt
Even if breach occurs, immutable backups enable recovery in hours
Total impact: $0 in breach costs
Business continues operating: Indefinitely
The Math
Reactive approach: Save thousands, lose millions, close business.
Proactive approach: Invest thousands, prevent millions in losses, stay in business.
Cost multiplier: 10x to 100x or more.
The "we can't afford security" mindset should actually be: "We can't afford NOT to have security."
The Personal Math: Streaming Services vs. Security
The same false economy affects individuals.
The Streaming Service Comparison
Most people across North America spend more on streaming services each month than they would on comprehensive cybersecurity protection.
Netflix, Spotify, Disney+, HBO, Amazon Prime—easily $50-80 USD/month combined.
Comprehensive personal cybersecurity protection? Often less than a single streaming subscription.
But when identity theft hits and you lose $7,600+ USD (or $10,000+, or $100,000+), that Netflix subscription won't seem like such a priority anymore.
What Prevention Actually Costs
We're not going to quote specific vendor pricing because it varies, but here are the categories of protection available:
Password manager: Prevents credential reuse across accounts
Multi-factor authentication: Often free, blocks most account takeovers
Mobile security solution: Protects credentials on phones/tablets
Credit monitoring service: Early warning system for identity theft
VPN for public WiFi: Prevents credential interception
The total monthly investment for comprehensive personal cybersecurity? Modest—far less than most people think.
What Loss Actually Costs
United States:
Average victim loss: $7,600 USD
37% of victims: $10,000+ USD
22% of victims: $100,000+ USD
3% of victims: $1 million+ USD
Canada:
Total losses: $638 million CAD in 2024
34,621 reported victims
Only 5-10% of fraud actually reported (real numbers far higher)
Plus:
Several weeks to months to recover control
Anxiety, depression, trust issues
Credit damage that lasts years
Emotional toll (16% contemplate suicide)
Time away from work and family dealing with fraud
The ROI of Prevention
Would invest: Modest monthly fees for comprehensive protection—typically less than streaming services.
Actually lost:$7,600+ USD average in the U.S., plus emotional trauma and time.
Return on investment: 20x to 100x or more.
And here's the kicker: Unlike subscription services, cybersecurity protection actually protects something valuable—your identity, your money, your livelihood.
The THINKFLEX Resilience-First Approach
At THINKFLEX, we've watched businesses and individuals make the same mistake repeatedly: they treat cybersecurity as something they'll deal with "if and when" it happens.
By the time it happens, it's too late.
Our approach is different: Build resilience first. React from strength, not crisis.
Prevention Layer: Stop Attacks Before They Succeed
Email Protection (Proofpoint + Red Sift DMARC): Business Email Compromise accounts for 73% of all cyber incidents and causes $2.9 billion USD in annual losses. Email is where most attacks start.
What we provide:
Advanced threat detection beyond basic spam filtering
DMARC enforcement to prevent domain spoofing
Protection against phishing, malware, and BEC attacks
Credential theft prevention
Security Awareness Training:60% of breaches involve the human element. Your people are either your strongest defense or your weakest link.
What we provide:
Regular, documented employee training
Phishing simulations with real-world scenarios
Awareness of social engineering tactics
Culture of security consciousness
Multi-Factor Authentication Deployment:56% of BEC victims didn't use MFA on their email accounts at the time of attack. MFA blocks the vast majority of credential-based attacks.
What we provide:
MFA implementation across all critical systems
Phishing-resistant authentication methods
Integration with existing infrastructure
Mobile Threat Defense:22% of breaches start with stolen credentials, and mobile devices are increasingly the source. Your employees use phones for work email, multi-factor authentication, and accessing corporate systems.
What we provide:
Network threat detection on mobile devices
Malicious app prevention
Credential protection without invasive MDM
Privacy-respecting monitoring
Detection Layer: Find Threats Fast When They Occur
Managed Endpoint Detection and Response (Huntress EDR): Attackers are in your network for an average of nearly six months before detection. Every day they're inside is another day of data theft and system compromise.
What we provide:
24/7 endpoint monitoring and threat detection
Automated response to contain threats
Real-time visibility into endpoint activity
Threat hunting and investigation
Managed SIEM (Security Information and Event Management): Centralized visibility across your entire environment to spot anomalies and coordinate response.
What we provide:
Centralized log collection and analysis
Correlation of events across systems
Real-time alerting on suspicious activity
Compliance and audit trail
Managed ITDR (Identity Threat Detection and Response):91% of organizations reported an identity-related breach in the past year. Your identities—user accounts, credentials, access rights—are the #1 attack surface.
What we provide:
Continuous identity monitoring
Detection of credential compromise
Anomalous access pattern identification
Rapid response to identity threats
Recovery Layer: Restore Operations Without Paying Ransoms
Backup & Disaster Recovery (N-able Cove):14% of ransomware victims had their backup storage also encrypted or made inaccessible. If attackers compromise your backups, ransomware becomes your only option—unless your backups are truly protected.
What we provide:
Immutable, encrypted backups that can't be altered or deleted
Tested restoration procedures with documented recovery capabilities
Independence from ransomware demands
Self-recovery without insurance delays
Incident Response Planning:70% of organizations lack dedicated procedures for verifying transfer requests, making them vulnerable to BEC. When an incident occurs, chaos costs you time, money, and data.
What we provide (via vCIO Services):
Documented incident response plans
Contact trees and escalation procedures
Tabletop exercises to test response
Playbooks for common scenarios
Evidence management for investigations
Advisory Layer: Strategic Resilience Architecture
Virtual CIO Services: Cybersecurity isn't just about tools—it's about strategy, policies, documentation, and integration.
What we provide:
Security policy development and documentation
Compliance requirements management
Integration of security controls across environment
Evidence management for audits and renewals
Strategic planning for resilience
The Outcome
When you build resilience first:
Lower risk: Attacks are prevented before they cause damage
Faster recovery: If something does get through, you contain and recover in hours/days, not weeks/months
Better insurance terms (if needed): Strong security posture qualifies you for better rates and coverage
Complete control during incidents: You're not waiting for insurance adjusters or paying deductibles on top of premiums
You're not at the mercy of whether a claim gets approved (remember: 40% of cyber insurance claims are denied). You're not gambling on a 22% chance that a BEC attack succeeds.
You're resilient. Independent. Prepared.
The Choice: Pay Now or Pay Later
Your LinkedIn profile is already out there. 4.3 billion professional records were exposed in November 2025 alone, enriched with 429 billion correlated attributes. 500 million LinkedIn profiles are actively being sold on dark web forums.
Your credentials are probably compromised. 94 billion credentials and cookies were exposed in just two years, and 68.89% of breached passwords are now available in plaintext.
Your organization is a target. Small businesses are targeted four times more often than enterprises, and across North America:
You have two choices:
Option 1: Reactive Security (Penny-Wise, Pound-Foolish)
Skip proactive security to "save money"
Hope you don't get breached
When (not if) you get breached: pay 10-100x more in response costs
United States: Average breach cost $10.22 million USD
Canada: Average breach cost $6.98 million CAD
If you're a small business: High chance you close permanently
If you're an individual: $7,600+ USD average loss, with 37% losing $10,000+
Weeks to months of recovery time
Emotional trauma, trust issues, constant fear
The math: Save thousands on security. Lose millions to breaches. Potentially lose everything.
Option 2: Resilience-First Security
Invest in prevention, detection, and recovery (typically tax-deductible business expenses)
Stop attacks before they succeed
Detect threats in hours/days, not months
Recover without paying ransoms or relying on insurance claims
Maintain business continuity
Protect personal and professional reputation
Sleep at night
The math: Invest thousands in protection. Prevent millions in losses. Stay in business. Protect your life.
Consider this: You already spend money on things far less critical than protecting your business, your identity, and your livelihood. Office coffee. Streaming services. Software you barely use.
Cybersecurity isn't an expense—it's insurance you hope never to need but can't afford to skip.
Stop Reacting. Start Building Resilience.
The average LinkedIn profile contains everything an attacker needs to craft a convincing BEC attack worth $125,000+ USD. Your credentials are probably already for sale on the dark web. Your organization is being scanned right now for vulnerabilities.
The question isn't "will we be targeted?"
The question is: "When we're targeted, will we survive?"
If you're building resilience first—prevention, detection, recovery—the answer is yes.
If you're waiting to react until after you're breached, the statistics are clear across North America:
United States: Average breach cost $10.22 million USD
Canada: Average breach cost $6.98 million CAD
Small businesses: High closure rates within months of major breaches
Individuals: $7,600+ USD average loss, emotional trauma, months of recovery
Ready to stop reacting and start building resilience?
Contact THINKFLEX to discuss your cybersecurity strategy: THINKFLEX.ca
We help businesses and individuals across North America build prevention-first security that actually works—before they need it, not after it's too late.
References
IBM Cost of a Data Breach Report 2025 - Global, U.S., and Canadian breach costs, detection timelines, AI/automation impact - Source
IBM Canada: Data Security Under Increased Threat - Canadian breach costs ($6.98M CAD), financial sector impacts - Source
Verizon Data Breach Investigations Report (DBIR) 2025 - Attack vectors, ransomware prevalence, human element statistics - Source
FBI Internet Crime Complaint Center (IC3) - BEC losses, complaint data 2024-2025 (U.S.) - Source
Canadian Anti-Fraud Centre - Canadian fraud losses ($638M CAD in 2024), victim statistics - Source
Statistics Canada - Canadian business cybersecurity incidents, recovery spending ($1.2B CAD) - Source
Constella Intelligence: 2026 Identity Breach Report - Plaintext credential surge, infostealer data, identity density gap - Source
Identity Theft Resource Center (ITRC) - 2025 Data Breach Report, Consumer Impact Report (U.S.) - Source
SpyCloud: Cybersecurity Industry Statistics 2026 - Identity exposure, ATO, BEC statistics - Source
Cybernews - LinkedIn breach reporting, 500M profiles scraped - Source
Hoxhunt: Business Email Compromise Statistics 2025 - BEC attack volume, AI-generated phishing, success rates - Source
FTC / Experian - U.S. identity theft complaints, financial losses 2024-2025 - Source
Secureframe: Data Breach Statistics 2026 - Time to identify/contain, costs by attack vector - Source
Viking Cloud / SentinelOne - Cybersecurity statistics, industry-specific breach costs - Source
DeepStrike: Social Engineering Statistics 2025 - Phishing, BEC, human element impact - Source
AARP / Javelin - U.S. identity fraud losses, scam impact on victims - Source
LifeLock / Gen Digital - 1 in 4 Americans victimized, average losses - Source
StrongDM: Data Breach Statistics - Detection time, password uniqueness, breach costs - Source
Made in CA: Cyber Crime Statistics in Canada - Canadian cybersecurity statistics, company attack rates - Source