Security and technology expertise for everyone. Whether you're protecting your family, running a business, or managing enterprise IT, THINKFLEX covers what you need to know—threats, infrastructure, strategy, compliance, and everything in between. Expert insights. Real solutions.
BLOG
THINK
Your Computer's Cookie Problem Isn't Calories - It's Credentials
In June 2025, researchers uncovered 94 billion stolen browser cookies on the dark web—20% still active. These aren't just tracking cookies. They're session tokens: digital keys that let attackers access your accounts without passwords or two-factor authentication. Cookie theft is a booming criminal enterprise, and your browser is carrying the evidence.
What Happens When Your Employee Clicks That Link: A 72-Hour Timeline
It's 2:47 AM on a Wednesday when your phone vibrates. Jake's name glows on the screen—your part-time IT guy who normally comes in Tuesdays and Thursdays.
Your stomach drops before you're even fully awake.
"We have a situation," he says. "Sarah clicked a link yesterday morning. I just got an alert. Your server is encrypting files right now."
What follows isn't the Hollywood version. It's the real version—the exhausting, expensive 72 hours that could determine whether your 28-person business survives. By hour 6, you'll face a $45,000 ransom demand. By hour 72, you'll be $400,000 in debt. And it all started with one perfectly legitimate-looking email.
The Enemy Within: Why Insider Threats Are Harder to Stop Than Hackers
Your biggest security risk isn't a hoodie-wearing hacker in a basement. It's Janet from accounting. And your security stack can't see her. 83% of organizations experienced insider attacks in 2025. $19.5M average annual cost. Your perimeter defenses are working perfectly - the threat is already inside
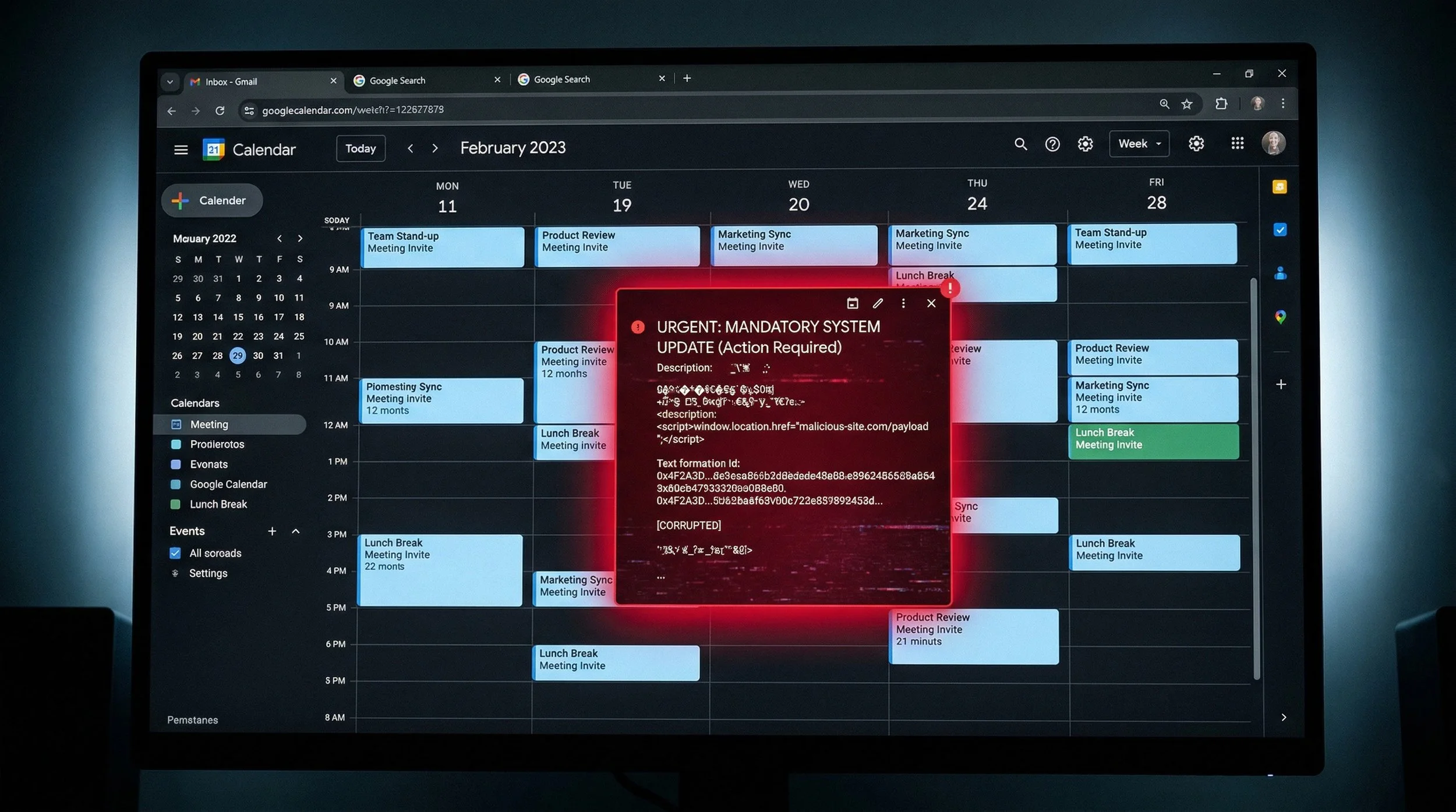
Hackers Are Hiding Malware in Your Calendar Invites
Security researchers discovered attackers weaponizing Google Calendar invites to steal confidential meeting data through Gemini AI manipulation. The attack requires no malware, no phishing email, and no credential theft - just a seemingly innocent calendar invite containing hidden instructions. When users ask Gemini about their schedule, the AI unknowingly executes these embedded commands, creating new calendar events filled with private meeting summaries and automatically sharing them with attackers. Traditional security controls - email gateways, endpoint protection, and data loss prevention - can't detect the attack because it uses legitimate Google services and authorized user credentials to exfiltrate data.
Your LinkedIn Profile Is Worth $50,000 to Hackers. What's It Worth to You?
Your LinkedIn profile contains everything hackers need to craft a $125,000 Business Email Compromise attack—your job title, your connections, your communication style, your travel schedule. With 4.3 billion professional records exposed in 2025 and enriched with 429 billion correlated attributes, your professional identity is being weaponized at industrial scale right now.
We'd Rather Stop a Breach Than Close a Sale: Why THINKFLEX Offers Complimentary Security Assessments
Your domain is publicly advertising security weaknesses right now. Attackers scan for these constantly. THINKFLEX offers complimentary external security assessments covering email authentication, credential exposure, website security, and compliance. No sales pressure. Just honest guidance. Because we'd rather stop a breach than close a sale.
The Cyber Insurance Catch-22: Perfect Security Required, Coverage Optional
Want cyber insurance in 2026? First, you'll need to prove you have MFA, EDR, immutable backups, incident response plans, security training, and more. Here's the catch: if you have all that, you've already built everything you need to prevent and recover from cyber incidents on your own.
Why Diversified Cybersecurity Portfolios Reduce Risk and Improve Resilience
Just as investors diversify to reduce risk, modern organizations benefit from a portfolio approach to cybersecurity. This article explains why diversification outperforms single-vendor strategies and how governance keeps complexity under control.
Protecting Your Privacy in a Digital World: A Modern Guide to Staying Safe, Smart, and Secure
Your voice, your photos, your movements, and even your habits can now be copied, analyzed, and used against you. Privacy is no longer something that fades in the background. It is something you must fight to protect. In this guide, we break down how attackers target you and what you can do today to prevent it.
Why Security Awareness Training Is One of Your Most Important Business Investments
This post explains why Security Awareness Training is essential from a business perspective. It also covers the HR and insurance viewpoints, provides guidance on training modules and recommended cadence, and highlights the importance of reporting, continuous phishing testing, and identifying weak users.