Security and technology expertise for everyone. Whether you're protecting your family, running a business, or managing enterprise IT, THINKFLEX covers what you need to know—threats, infrastructure, strategy, compliance, and everything in between. Expert insights. Real solutions.
BLOG
THINK
Email Is Still Your Biggest Risk (and your team isn't ready)
Your organization has invested in email filters and security controls. Yet attacks are still getting through. According to Proofpoint's 2026 report, 67% of security incidents involved email as the initial attack vector, and 63% of organizations cite email as their most common attack entry point.
Sextortion Scams: From Teen Targeting to Email Blackmail
The FBI received over 13,000 sextortion reports between October 2021 and March 2023, with at least 20 victims dying by suicide. This growing threat targets both teenagers through financial extortion and adults through mass email blackmail campaigns. If you have children online or you've received threatening emails claiming to have compromising footage, understanding how these scams work—and knowing that help is available—can save lives.
Does Your Domain Have an Evil Twin?
Domain squatting - attackers registering domains that look close enough to yours to fool people at a glance. They don't hack your email. They legitimately own lookalike domains you don't control: acme-industries.com (added hyphen), acmeindustries-portal.com (added suffix), acmeindustries.co (different TLD).
Most businesses don't know these domains exist until the damage is done. Learn how to find your domain's evil twin, register defensive variations, and protect your business from impersonation attacks.
Your IT Guy Just Quit. Now What?
Your IT person just gave two weeks' notice. They've been with you for years—the only one who knows your passwords, manages your servers, and handles everything technical. And now they're leaving.
This isn't just an HR issue. It's an institutional crisis.
Your Computer's Cookie Problem Isn't Calories - It's Credentials
In June 2025, researchers uncovered 94 billion stolen browser cookies on the dark web—20% still active. These aren't just tracking cookies. They're session tokens: digital keys that let attackers access your accounts without passwords or two-factor authentication. Cookie theft is a booming criminal enterprise, and your browser is carrying the evidence.
What Happens When Your Employee Clicks That Link: A 72-Hour Timeline
It's 2:47 AM on a Wednesday when your phone vibrates. Jake's name glows on the screen—your part-time IT guy who normally comes in Tuesdays and Thursdays.
Your stomach drops before you're even fully awake.
"We have a situation," he says. "Sarah clicked a link yesterday morning. I just got an alert. Your server is encrypting files right now."
What follows isn't the Hollywood version. It's the real version—the exhausting, expensive 72 hours that could determine whether your 28-person business survives. By hour 6, you'll face a $45,000 ransom demand. By hour 72, you'll be $400,000 in debt. And it all started with one perfectly legitimate-looking email.
The Enemy Within: Why Insider Threats Are Harder to Stop Than Hackers
Your biggest security risk isn't a hoodie-wearing hacker in a basement. It's Janet from accounting. And your security stack can't see her. 83% of organizations experienced insider attacks in 2025. $19.5M average annual cost. Your perimeter defenses are working perfectly - the threat is already inside
Attackers Are Impersonating Your Organization Right Now. Your Email Security Is Just Watching.
71% of domains have no email impersonation protection. Another 23% use DMARC p=none - "monitor only" mode that provides zero security. Business Email Compromise cost $2.7B in 2024. Learn why enforcement matters and how to actually stop attackers from spoofing your domain.
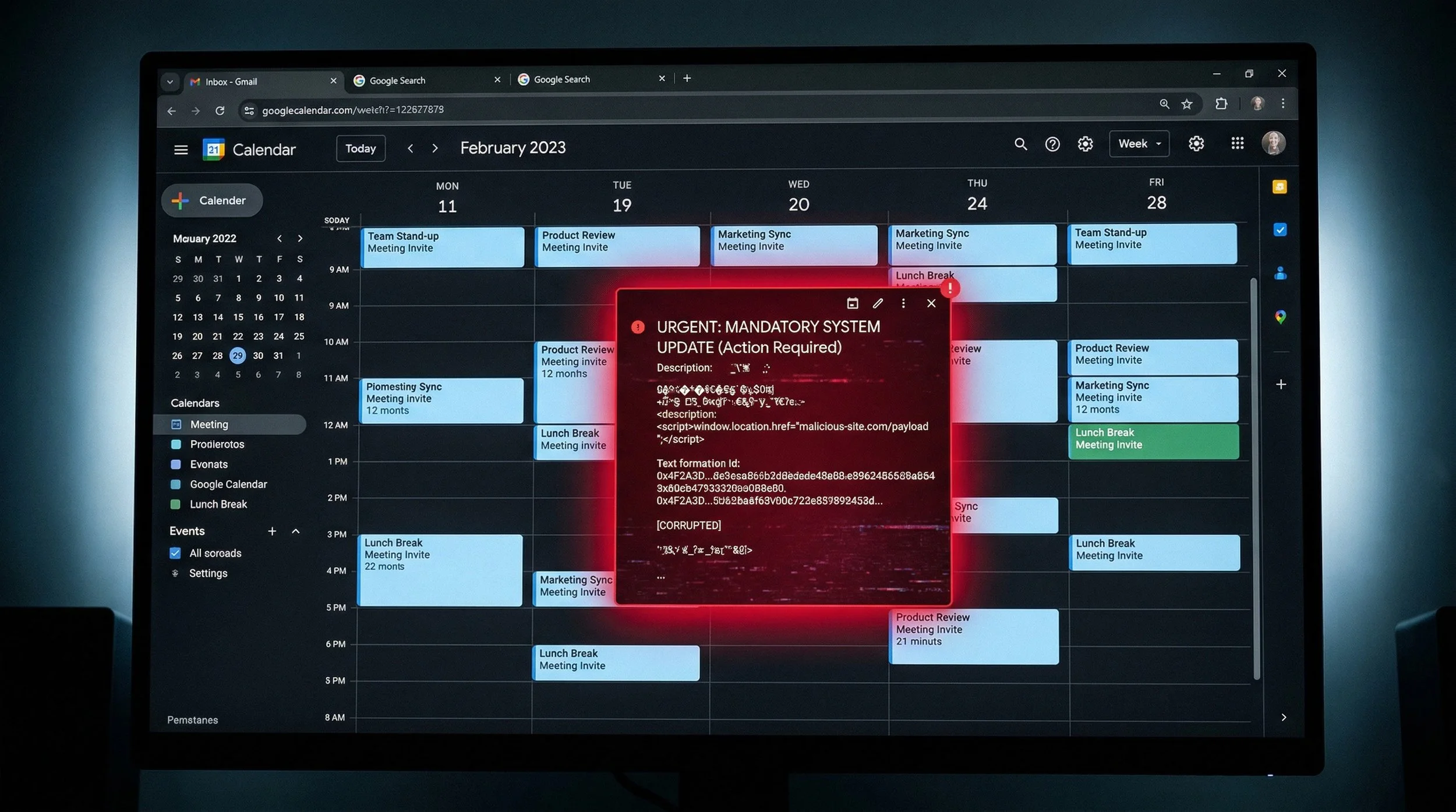
Hackers Are Hiding Malware in Your Calendar Invites
Security researchers discovered attackers weaponizing Google Calendar invites to steal confidential meeting data through Gemini AI manipulation. The attack requires no malware, no phishing email, and no credential theft - just a seemingly innocent calendar invite containing hidden instructions. When users ask Gemini about their schedule, the AI unknowingly executes these embedded commands, creating new calendar events filled with private meeting summaries and automatically sharing them with attackers. Traditional security controls - email gateways, endpoint protection, and data loss prevention - can't detect the attack because it uses legitimate Google services and authorized user credentials to exfiltrate data.
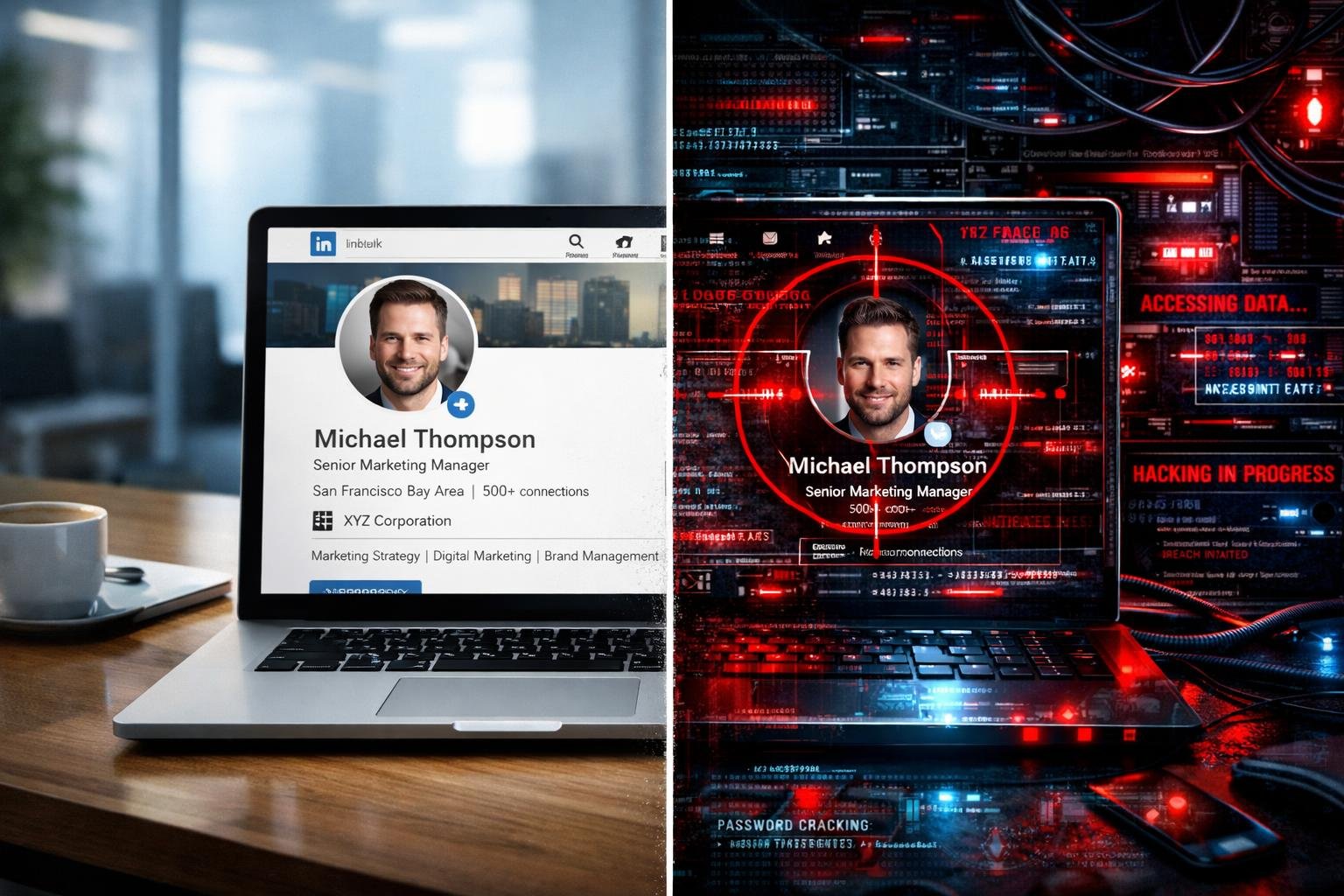
Your LinkedIn Profile Is Worth $50,000 to Hackers. What's It Worth to You?
Your LinkedIn profile contains everything hackers need to craft a $125,000 Business Email Compromise attack—your job title, your connections, your communication style, your travel schedule. With 4.3 billion professional records exposed in 2025 and enriched with 429 billion correlated attributes, your professional identity is being weaponized at industrial scale right now.
We'd Rather Stop a Breach Than Close a Sale: Why THINKFLEX Offers Complimentary Security Assessments
Your domain is publicly advertising security weaknesses right now. Attackers scan for these constantly. THINKFLEX offers complimentary external security assessments covering email authentication, credential exposure, website security, and compliance. No sales pressure. Just honest guidance. Because we'd rather stop a breach than close a sale.
The Cyber Insurance Catch-22: Perfect Security Required, Coverage Optional
Want cyber insurance in 2026? First, you'll need to prove you have MFA, EDR, immutable backups, incident response plans, security training, and more. Here's the catch: if you have all that, you've already built everything you need to prevent and recover from cyber incidents on your own.
The Leak in Your Pocket: Why Your Phone Needs Real Security (Not Just a Passcode)
Your phone knows more about you than your spouse does. Banking apps with saved credentials. Work email with client data. Photos with location metadata. Every WiFi network you've ever connected to.
And it's protected by... what exactly? A passcode? Face ID?
The BYOD Blind Spot: Securing Mobile Access Without Controlling Personal Devices
Your employee just logged into Microsoft 365 from their personal iPhone. They accessed your financial systems, checked Google Workspace, and downloaded client data. Your security team has absolutely no visibility into that device. No endpoint protection. No patch management. No way to know if that phone is compromised. Yet it has full access to your most critical systems.
Why Diversified Cybersecurity Portfolios Reduce Risk and Improve Resilience
Just as investors diversify to reduce risk, modern organizations benefit from a portfolio approach to cybersecurity. This article explains why diversification outperforms single-vendor strategies and how governance keeps complexity under control.
Enterprise Email Protection Platform Selection Guide for Modern IT Leadership
Enterprise email threats are evolving faster than traditional defenses can keep up. This guide outlines what modern IT leaders should look for when selecting an Enterprise Email Protection Platform, including essential security capabilities, integration requirements, architectural considerations, and vendor maturity signals.
Protecting Your Privacy in a Digital World: A Modern Guide to Staying Safe, Smart, and Secure
Your voice, your photos, your movements, and even your habits can now be copied, analyzed, and used against you. Privacy is no longer something that fades in the background. It is something you must fight to protect. In this guide, we break down how attackers target you and what you can do today to prevent it.
Why Every Business Needs a vCIO: The Strategic Advantage of Virtual IT Leadership
A vCIO is not a technical contractor or an IT support role. They are a strategic partner who elevates your technology from a cost center into a business enabler. They bring structure to chaos, reduce risk, protect your data, support your people, and ensure every technology decision aligns with the long-term vision of the organization.
Why Security Awareness Training Is One of Your Most Important Business Investments
This post explains why Security Awareness Training is essential from a business perspective. It also covers the HR and insurance viewpoints, provides guidance on training modules and recommended cadence, and highlights the importance of reporting, continuous phishing testing, and identifying weak users.
The Importance of DMARC Protection: Stopping Email Impersonation Before It Starts
Email impersonation is one of the most effective—and overlooked—cyber threats facing organizations today. DMARC protection ensures only legitimate messages are sent from your domain, blocking spoofing and brand abuse before it reaches inboxes. It’s not just a technical safeguard—it’s essential to maintaining trust, compliance, and business credibility.